The compliance system of record for financial institutions.
Push events. We orchestrate. Your examiners read one audit trail.
The problem
Compliance teams are firefighting across five tools while a regulator waits.
The cost of fragmentation is not slow workflows. It is the inability to answer the regulator with confidence.
01
A regulatory deadline you cannot push
CBN circular BSD/DIR/PUB/LAB/019/002 requires every regulated FI to file a roadmap by 10 June 2026 and stand up a CBR-aligned monitoring infrastructure. Most institutions have nothing approaching that.
02
A stack that does not talk to itself
Sumsub for KYC. ComplyAdvantage for sanctions. A spreadsheet for case work. A core banking event firehose nobody listens to. Five tools, one regulator, no audit trail anyone wants to defend.
03
No system of record for examiners
When the examiner asks "why was this customer flagged, who reviewed it, what did the rule say at that moment, and where is the evidence" you need one answer, not five exports.
How it works
You push raw events. We hold the state.
Your engineering responsibility ends at sending data and reacting to operational hooks. WhoComply owns the resulting compliance state, the unified customer risk view, alerts, cases, reports, and the audit trail.
Inbound
What you push into WhoComply
Customer profiles
POST /customersWhen onboarding happens or KYC details change.
Transaction events
POST /events/webhookEvery event that should drive scoring. Pipeline runs immediately.
Native ledger postings
POST /postingsRecording funds movements directly. Double-entry, hash-chained, signed.
Outbound
What WhoComply sends back
Risk view reads
GET /customers/{id}/risk-viewTransaction-time decisioning. Rating, score, sanctions, EDD.
Webhook subscriptions
POST /webhooksSubscribe to alert.created, alert.resolved, alert.dismissed.
Examiner audit reads
GET /auditHash-chained audit log. Immutable, deterministic, defensible.
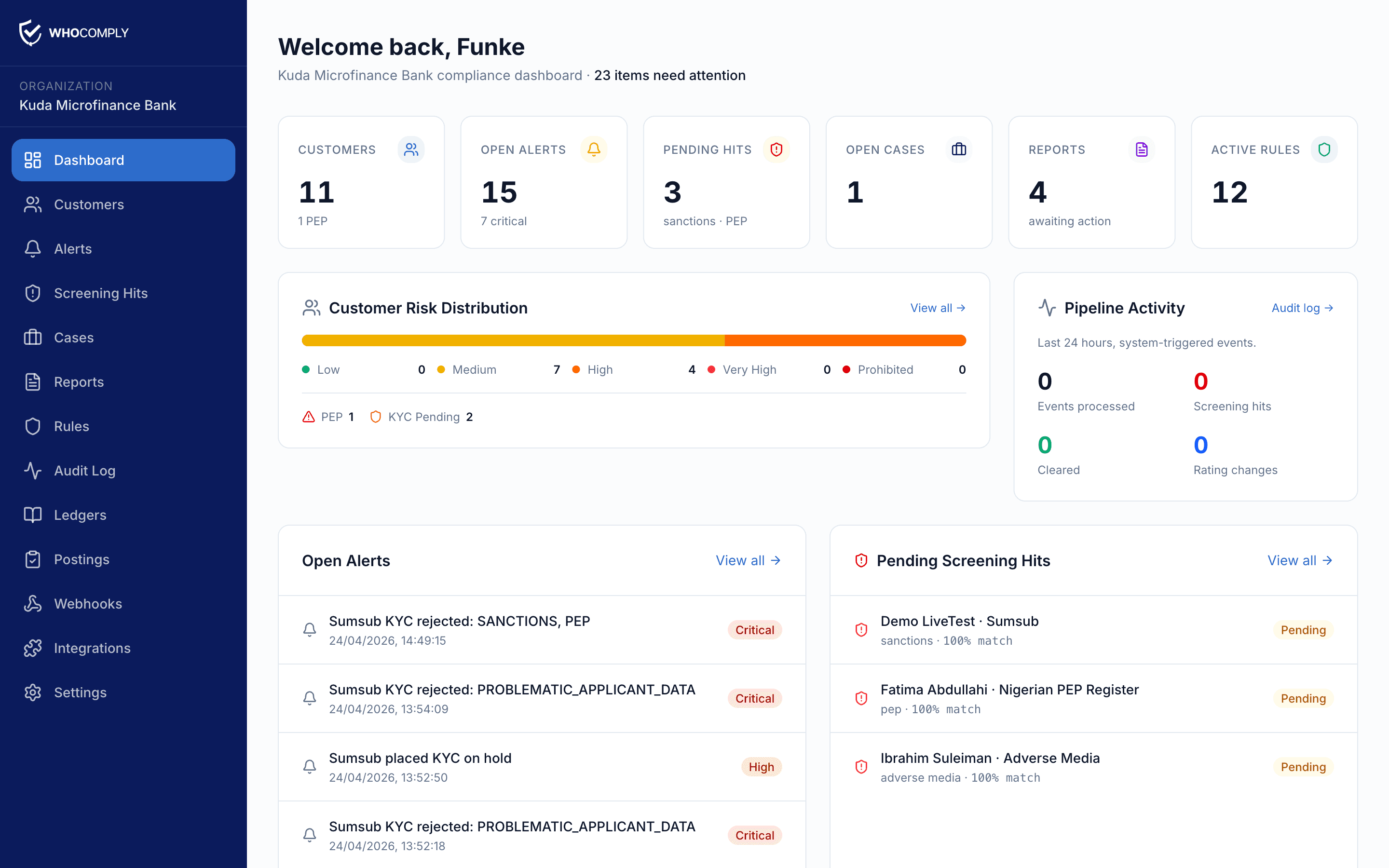
Triage, case management, report filing, and provider activation all happen inside the WhoComply dashboard. Your engineering team does not need to build a parallel UI.
The pipeline
Six stages run on every event. Deterministic. Auditable. Fast.
Match the event to a customer.
Every inbound event lands with an account ref, a KYC ref, or a tenant-scoped customer UUID. The resolver maps it deterministically. No fuzzy matching, no orphaned events.
Resolve
Pull the live state.
Risk profile, prior alerts, watchlist matches, the rule scope this customer is subject to. Everything downstream stages need is read once, in one transaction.
Load profile
Sanctions, PEP, adverse media.
Native screening or a plugin adapter. OFAC, UN, EU, NG PEP register. Hits become alerts with provenance. The original payload is hashed, signed, and stored.
Screen
Run the rule engine.
Velocity, threshold, structuring, geography, peer-group anomalies. Rules are versioned. The rule snapshot at the moment of evaluation is captured against every alert.
Monitor
Update the composite.
Identity, behavioral, transactional axes feed one composite score. A rating change fans out through the risk view, the EDD trigger, and the webhook stream.
Score
Write, fan out, audit.
Alerts saved. Risk view refreshed. Webhooks queued with HMAC signatures. The audit log gets a new hash-chained entry. The whole pipeline is replayable.
Persist
Adebayo M.
High risk · KYC ok
alert.created
risk.changed
webhook.queued
audit.append
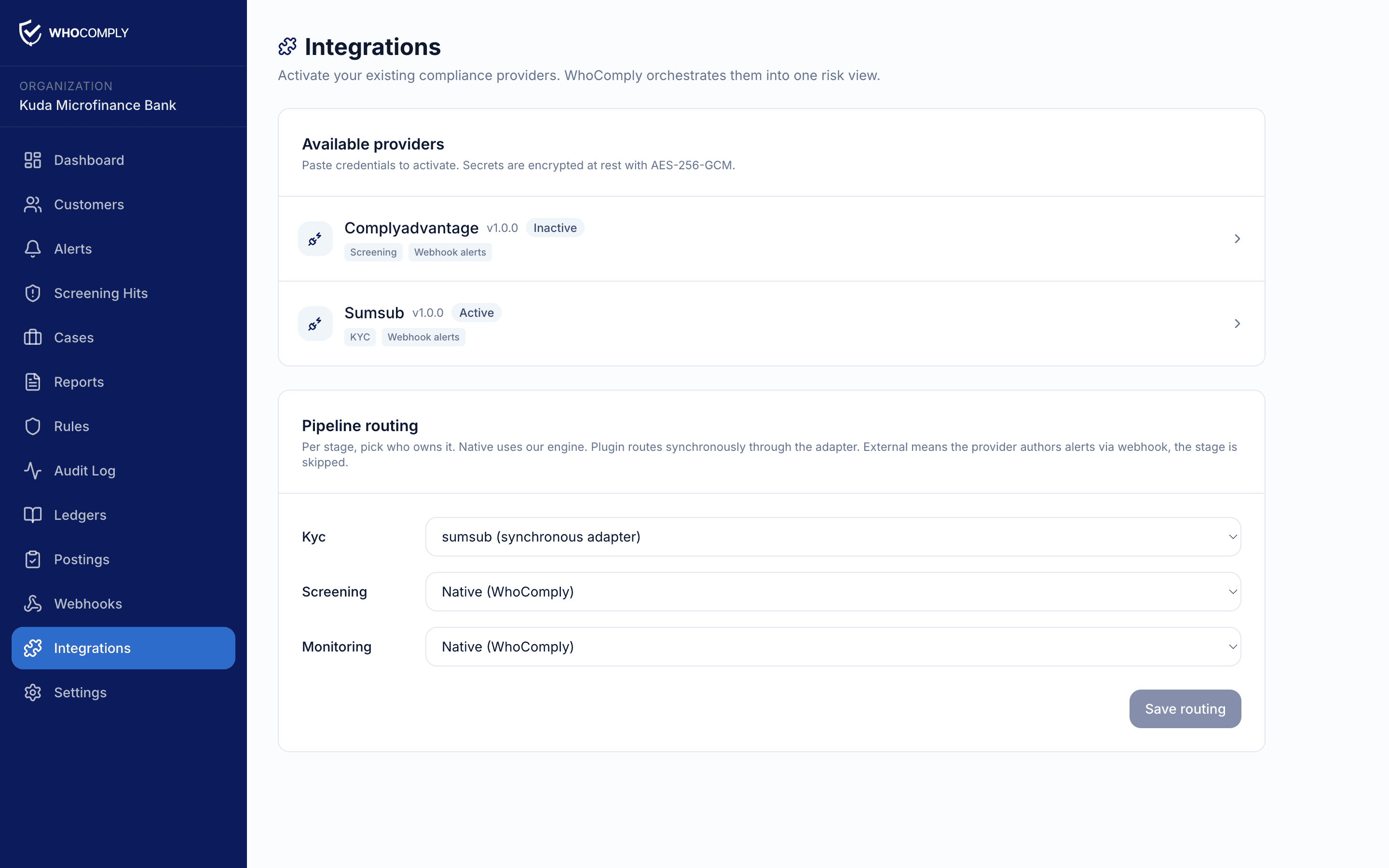
Activate without engineering
Plug in the providers your team already uses.
Your compliance admin pastes credentials in the dashboard. The plugin authors alerts. The pipeline reads the right adapter at run time. Engineering writes nothing.
Sumsub
KYC · KYB
ComplyAdvantage
Screening · PEP
Smile ID
Identity
Mono
Open Banking
Paystack
Card Detail
Onfido
KYC
Native engines
Three engines, first-class, when you do not want to outsource the substance.
Plug-ins are optional. The native ledger, monitoring engine, and reporting engine are first-class. Most institutions run a mix.
Native ledger
Double-entry, hash-chained, signed.
When your core banking is not the system of record for funds, post directly to WhoComply. Every transaction is double-entry. Every block is hash-chained. Every signature is HMAC-verifiable. The examiner reads one tape.
Monitoring engine
A rule DSL your compliance team can read.
Velocity, threshold, geography, structuring, peer-group anomalies. Rules are versioned, scoped to customer segments, and run deterministically against every event. Triggered alerts carry the rule snapshot for audit.
Reporting engine
NFIU goAML XML, generated and signed.
STR, SAR, CTR, FTR. Reports compose from the live state, follow maker-checker review, and emit goAML-conformant XML. Submission timestamps and reference numbers are recorded against the originating alerts.
Regulatory coverage
Built section by section against the CBN circular.
BSD/DIR/PUB/LAB/019/002 is the spec. Every section that demands a system control maps to a feature in WhoComply, with the audit evidence to defend it.
Book a demo
See your real customer data inside WhoComply in 30 minutes.
Bring your Sumsub or ComplyAdvantage credentials. We will walk through ingesting a live event end to end. No pre-call form, no NDA.
30 min
Live walkthrough on your data
0 LOC
No code change to see ingestion
10 Jun 2026
CBN roadmap deadline we hit together